ZTP short for Zero Touch Provisioning is one of the instrumental parts of an end-to-end network automation ecosystem, which counts for a fast, reliable, and error-free provisioning of new as well as existing network devices. Network Operators, be it a Service Provider, an Enterprise and others spent a great amount of time throughout the last decades when it comes to introducing a new router or a switch to a network, and it mainly included couple of steps to follow, such as; plan, prepare, install and report the status of the new device. As such, I believe ZTP is a great mechanism that the network operators will benefit from.
Looking at it closely, with ZTP you spend some time in the beginning by setting-up your network management system (DHCP and HTTP server) for the purpose of automating the whole process of discovering the network device, installing the necessary software and applying initial or full configuration to the device.
I don’t want to emphasise much on the cost savings while using ZTP but the truth is; you don’t really need a skilled person to go on-site and bring-up the router anymore. Anyone can do it, as long as he/she is able to plug in the power cable, and physically connect the Management port, the rest is just a Magic.
There are many valuable articles about ZTP out there and I recommend you to check them out, while my focus here is to explain the whole process in a much simpler way and straight to the point.
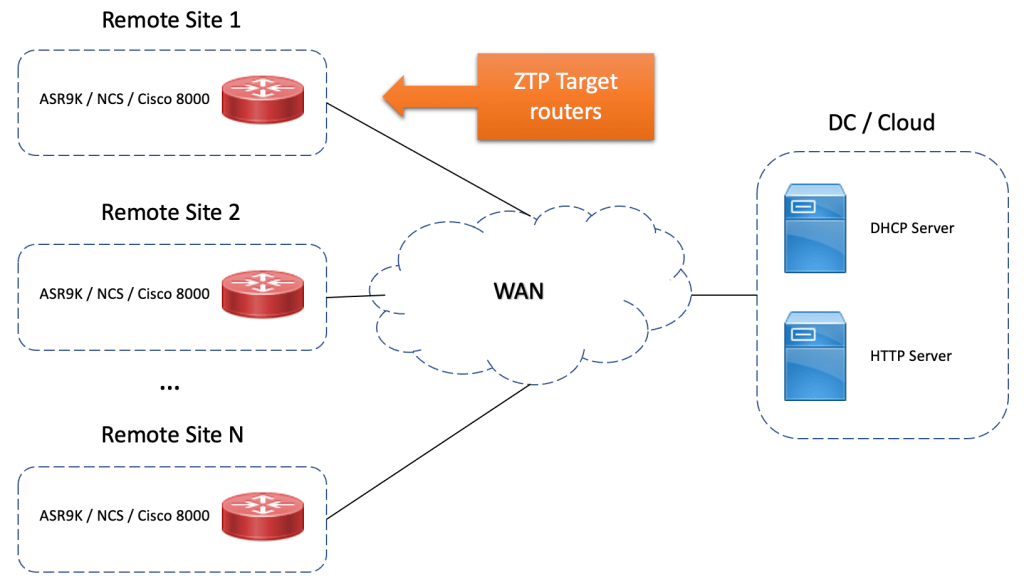
Assuming we have couple of remote sites (the device in RED is our target device that we want to auto-provision) as depicted below, this could be a PE device, a CPE device, or a remote PoP with local P routers. On the other side (datacenter or some cloud based hosted service) we need a DHCP server as well as HTTP server.
Cisco IOS-XR as well as IOS-XE based platforms have built-in Linux and/or Guest-shell capabilities due to their non-monolithic architecture of the operating system. This is quite an advantage that provides unprecedented capabilities in terms of; What and How much you can do with IOS-XR nowadays. And that advantage we are going to use to automate the bring-up and configuration process of a new router that has been shipped on a remote site without any pre-configuration at all, and ready for rollout.
Alright, let’s see what exactly the role of each component being part of the ZTP solution is:
DHCP Server provides:
- Name and location of IOS-XR image to be loaded
- Name and location of the custom (bash) script to be executed
- Name and location of configuration file
HTTP server provides:
- IOS-XR image
- IOS-XR packages
- Bash or Python script to be executed by ZTP (target router)
And following is a high-level workflow of ZTP process on an IOS-XR based router:

Based on the workflow diagram above, let’s see exactly what happens at each step:
1) Power ON: No brainer here, just power-on the router.
2) iPXE: During the booting process of the IOS-XR platform, it provides the possibility to boot the router from 4 different sources as below:
Please select the operating system and the boot device:
1) Boot to ROMMON
2) IOS-XR 64 bit Boot previously installed image
3) IOS-XR 64 bit Mgmt Network boot using DHCP server
4) IOS-XR 64 bit Mgmt Network boot using local settings (iPXE)
Selection [1/2/3/4]: 4Obviously, in this case the iPXE option needs to be selected from the menu. In this step the router sends a DHCP request, and gets a response from DHCP Server with Option-67, IPv4 address plus the path to download the base IOS-XR image. Below is the dhcpd.conf file running on DHCP server.
#dhcpd.conf
host ASR9000 {
hardware ethernet aa:bb:cc:dd:ee:ff;
fixed-address 10.0.0.10;
if exists user-class and option user-class = "iPXE" {
filename = "http://10.100.100.50/file/asr9k-mini-x64-6.6.3.iso";
} else if exists user-class and option user-class = "exr-config" {
filename "http://10.100.100.50/file/9000_ztp.sh";
}
}
}
3) Install IOS-XR: In this step, the router downloads the base IOS-XR image from HTTP server based on the information received from DHCP Server in step-2. Once download is complete, the router automatically installs the new IOS-XR software (take a coffee and enjoy a couple of minutes while the router automatically installs the software).
4) Install XR packages: Here starts the real fun. After software has been successfully installed and committed, the router initiates the request to download the ‘ZTP.sh’ script (check below for more info about ZTP script) from HTTP server (assuming the script has been uploaded upfront). This is a Linux based bash script, as such it runs on the integrated Linux shell environment in IOS-XR platform. And, as you will see below, the script contains all the necessary informations about the location of the packages (such as; OSPF, ISIS, MPLS, etc), downloading and installing them one-by-one automatically, including the possibility to generate the crypto keys for SSH purposes.
#!/bin/bash
################################################################################
# Install config and additional packages
################################################################################
source /disk0:/ztp/ztp_helper.sh
export HTTP_SERVER=http://10.100.100.1
export RPM_PATH="file/packages"
export CONFIG_PATH="file"
#Config
export INITIAL_CONFIG="9000_Day0.txt"
#Packages with RPM extension
K9SEC_RPM=asr9k-k9sec-x64-2.1.0.0-r663.x86_64.rpm
MCAST_RPM=asr9k-mcast-x64-2.0.0.0-r663.x86_64.rpm
ISIS_RPM=asr9k-isis-x64-1.1.0.0-r663.x86_64.rpm
OPTIC_RPM=asr9k-optic-x64-1.0.0.0-r663.x86_64.rpm
MGBL_RPM=asr9k-mgbl-x64-2.0.0.0-r663.x86_64.rpm
MPLS_RPM=asr9k-mpls-x64-2.0.0.0-r663.x86_64.rpm
MPLSTE_RPM=asr9k-mpls-te-rsvp-x64-2.1.0.0-r663.x86_64.rpm
#Packages without RPM extension
K9SEC_PACK=asr9k-k9sec-x64-2.1.0.0-r663
MCAST_PACK=asr9k-mcast-x64-2.0.0.0-r663
ISIS_PACK=asr9k-isis-x64-1.1.0.0-r663
OPTIC_PACK=asr9k-optic-x64-1.0.0.0-r663
MGBL_PACK=asr9k-mgbl-x64-2.0.0.0-r663
MPLS_PACK=asr9k-mpls-x64-2.0.0.0-r663
MPLSTE_PACK=asr9k-mpls-te-rsvp-x64-2.1.0.0-r663
function download_config(){
ip netns exec tpnns /usr/bin/wget ${HTTP_SERVER}/${CONFIG_PATH}/${FINAL_CONFIG} -O /harddisk:/new-config 2>&1
if [[ "$?" != 0 ]]; then
printf "### Error downloading system configuration ###"
else
printf "### Downloading system configuration complete ###";
fi
}
function apply_config(){
# Applies initial configuration
printf "### Applying initial system configuration ###";
xrapply_with_reason "Initial ZTP configuration" /harddisk:/new-config 2>&1;
printf "### Checking for errors ###";
local config_status=$(xrcmd "show configuration failed");
if [[ $config_status ]]; then
echo $config_status
printf "!!! Error encounter applying configuration file, review the log !!!!";
fi
printf "### Applying system configuration complete ###";
}
function install_pkg(){
#Download packages
printf "Downloading Packages"
ip netns exec tpnns /usr/bin/wget ${HTTP_SERVER}/${RPM_PATH}/${K9SEC_RPM} -O /harddisk:/$K9SEC_RPM 2>&1
if [[ "$?" != 0 ]]; then
printf "### Error downloading $K9SEC_RPM ###"
else
printf "### Downloading $K9SEC_PKG complete ###";
fi
printf "Downloading Packages"
ip netns exec tpnns /usr/bin/wget ${HTTP_SERVER}/${RPM_PATH}/${MPLSTE_RPM} -O /harddisk:/$MPLSTE_RPM 2>&1
if [[ "$?" != 0 ]]; then
printf "### Error downloading $MPLSTE_RPM ###"
else
printf "### Downloading $MPLSTE_RPM complete ###";
fi
xrcmd "install add source /harddisk:/ $K9SEC_RPM $MCAST_RPM $ISIS_RPM $OPTIC_RPM $MGBL_RPM $MPLS_RPM $MPLSTE_RPM" 2>&1
xrcmd "install activate $K9SEC_PACK $MCAST_PACK $ISIS_PACK $OPTIC_PACK $MGBL_PACK $MPLS_PACK $MPLSTE_PACK" 2>&1
local complete=0
while [ "$complete" = 0 ]; do
complete=`xrcmd "show install active" | grep k9sec | head -n1 | wc -l`
printf "Waiting for k9sec package to be activated"
sleep 5
done
rm -f /harddisk:/$K9SEC_RPM /harddisk:/$MCAST_RPM /harddisk:/$ISIS_RPM /harddisk:/$OPTIC_RPM /harddisk:/$MGBL_RPM /harddisk:/$MPLSTE_RPM /harddisk:/$MPLS_RPM
printf "### XR PACKAGE INSTALL COMPLETE ###"
if [[ -z $(xrcmd "show crypto key mypubkey rsa") ]]; then
echo "1024" | xrcmd "crypto key generate rsa"
else
echo -ne "yes\n 1024\n" | xrcmd "crypto key generate rsa"
fi
printf "### XR CRYPTO KEY GENERATED SUCCESSFULLY ###"
}
printf "Start Auto provision"
install_pkg;
download_config;
apply_config;
xrcmd "install commit"5) Download and apply Day-0 configuration: After the XR packages have been successfully installed and committed, and based on the script, the router will try to download the IOS-XR Day-0 configuration file from HTTP server. Again, it is crucial to prepare the Day-0 configuration upfront and set it up correctly on HTTP server. The router will then try to apply and commit the configuration file, and once it succeeds, the router should be up and running with minimal configuration, and if desired you can tweak the last step by applying the Day-1 (e.g; IGP) or Day-2 (e.g; Services/Customer).
If everything went well until the last step, it means you did it, congrats.
To make it more interesting and extend the ‘automation possibilities’, you might want to add into the game a Network Orchestrator such as the Cisco NSO, and a Network Controller such as SR-PCE. Having a way to bring-up a router from scratch and configure it automatically for remote management access, and then kicking-in with NSO to orchestrate the provision of new services and having the controller do the Path-Optimization is the future. Human errors should be a ‘yesterday thing’, nowadays, I prefer to say; let the system do the configuration-monkey job, while you focus on more important design related tasks.
Categories: General Networking
Leave a Reply